If you follow Microsoft products, then you may know about Microsoft Ignite. Held annually, it generates many exciting updates and announcements in the Microsoft world.
Microsoft held its most recent conference last October. In the rush of the recent holidays, you may have missed some of the highlights. So, we’re bringing them to you now.
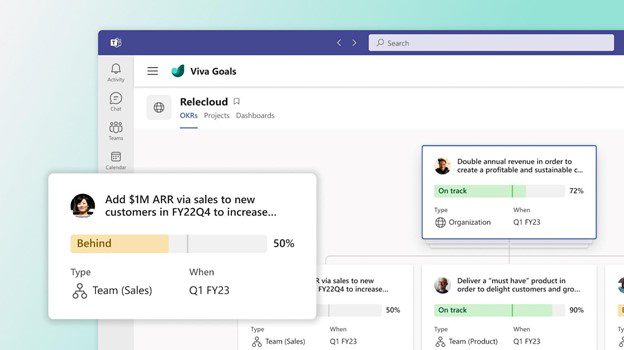
One thing you’ll notice is that Microsoft Teams got a lot of love at the event. Microsoft is now describing Teams as “the app at the center of Microsoft 365.” We can see why the company keeps enhancing this virtual workspace. Teams now has over 280 million users. It’s not surprising seeing that Microsoft has introduced over 450 new Teams features. And that’s just in the last year.
We’ll go over some Teams features below, along with other Microsoft App announcements from Ignite. These may give you some ideas for your next digital workflow upgrade.
Teams Premium
There is a new Teams Premium offering from Microsoft that adds a whole new AI component to the platform. This service includes several AI-powered features. They make it seem like you have your own meeting assistant.
Some of the cool features include automatically generating chapters from a Teams meeting. The app also generates personalized highlights for you. This saves you from having to rewatch the meeting later.
If you’re meeting internationally, you can enjoy real-time translations for captions. Meeting guides is another new feature. It sets up your meeting options according to your needs.
360-Degree Intelligent Camera for Teams Meetings
SmartVision 60 is the first 360-degree, center-of-room intelligent camera. It has the ability to track the speaker as they’re moving. The camera is also due to have a people recognition feature coming soon.
Virtual meetings can feel much more like real meetings using SmartVision 60. Instead of just seeing a small video feed of one person, the movement of the camera can capture a whole team.
Cisco is Now a Certified Devices Partner for Teams Rooms
Those that are fans of Cisco meeting products will be pleased to know they now have more options. Microsoft announced that Cisco is now a Teams Room Certified Devices partner. You can now start Teams meetings across all certified Cisco meeting devices.
Microsoft Places
One of the virtual workspace apps to support the new hybrid movement is Microsoft Places. This is a team management app that integrates with the rest of the Microsoft 365 ecosystem.
The office is still around, but for how long? Much of the world had to do things virtually during the pandemic. Many companies and employees found they like it better that way. Seventy-four percent of US companies have or plan to put in place a permanent hybrid work model.
Microsoft Places is one more way Microsoft is leading the hybrid office revolution. Some of the app’s features include:
- Manage and track where employees are working (at home or in the office)
- Track whether coworkers are away or available
- Track physical room use to make strategic decisions
Hours & Location Feature in Outlook & Teams
Another feature announcement related to the hybrid working world is hours and location. This is a new capability added to Teams and Outlook to make it easier to schedule in-person meetings.
It can get tricky to plan in-person meetings when you don’t know who is working at the office and who is remote. If you plan without checking, you’re bound to alienate someone. They won’t be happy if they were planning to work from home that day.
The new hours and location feature allows people to specify where they are working. They can adjust this from hour to hour. It takes the guesswork out of scheduling.
Loop App Private Preview
Another exciting app announcement that Microsoft made was about its Loop app. It stated that Loop entered private preview. This gives some organizations a chance to check it out.
Loop is a collaborative workspace app that helps teams ideate in a virtual space. All data pulled in from Microsoft 365 apps syncs automatically to stay up to date.
Microsoft Clipchamp Video Editor
You may have noticed an unfamiliar app popping up on Windows. Microsoft Clipchamp was formally announced at the Ignite event. It’s a quick and easy video editor for Windows PCs.
Have you ever felt frustrated trying to fix a video and not having the right tool to do it? Then you may want to take a closer look at what Clipchamp has to offer. It looks to have a fairly low learning curve.
Get Help Navigating the Microsoft 365 Universe
Microsoft 365 has come a long way in a short period. There are many different app integrations you can use to power your workflow. But it can get a bit complicated without an expert to help. Give us a call today to schedule a Microsoft consultation.
This Article has been Republished with Permission from .