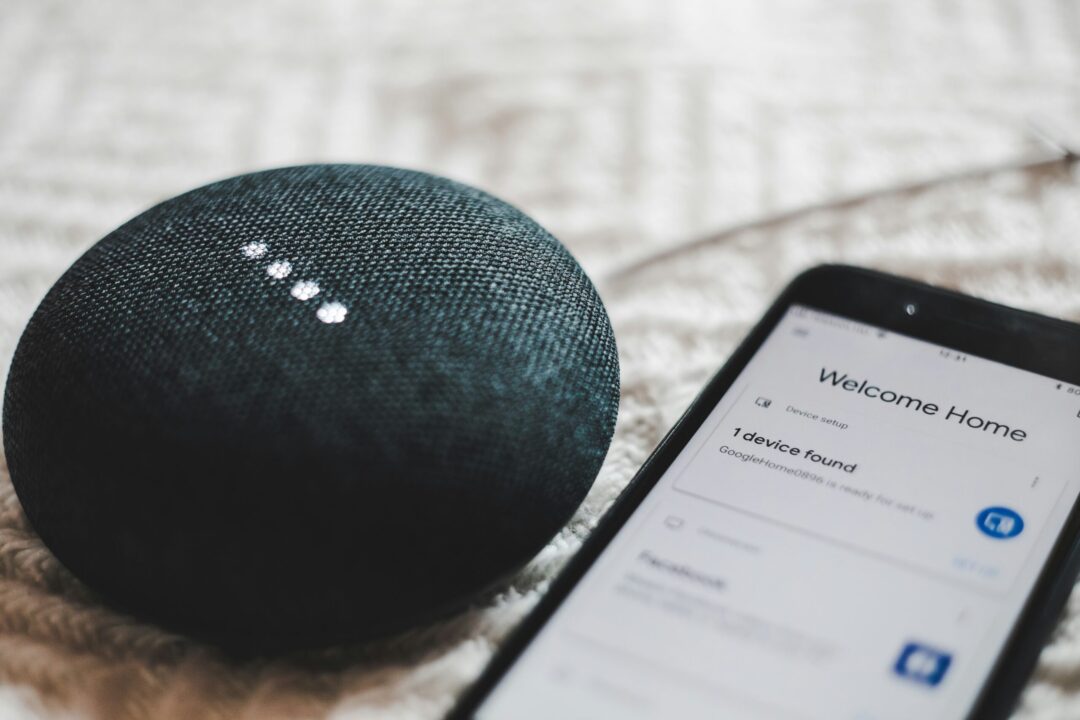
Imagine a world where your lights turn on automatically as you walk in the door. Your coffee starts brewing before you even crawl out of bed. A simple voice command adjusts the temperature to your perfect setting.
This is no longer just something out of a sci-fi movie. Today’s smart technology seamlessly integrates with your daily life. It can create a more convenient, comfortable, and even secure living space.
But wait, haven’t smart homes always been synonymous with hefty price tags? Not necessarily. Some high-end smart home systems can indeed cost a small fortune. But building a smart home on a budget is absolutely achievable.
Here are some tips to transform your humble abode into a tech-savvy haven affordably:
The Wellness Revolution: Gadgets for a Healthier, Happier You
1. Start Small and Scale Up
You don’t need to overhaul your entire home at once. First, identify areas where smart tech can make a significant impact on your routine. For example, do you constantly forget to turn off the lights? Smart bulbs are a budget-friendly solution. They can automate lighting as well as sync with a voice assistant for hands-free control.
2. Think Beyond the Big Brands
Major tech companies dominate the smart home market. But there are many affordable alternatives from lesser-known brands that offer similar functionality. Explore online marketplaces. Read reviews to find smart plugs, sensors, and other devices that fit your needs and budget.
3. Embrace the Power of DIY
For the tech-savvy individuals out there, consider DIY smart home solutions. There are readily available kits that allow you to build your own smart switches or sensors. Look for readily available online resources. This approach does need some technical know-how. But it can be a rewarding way to create a customized smart home experience at a fraction of the cost.
4. Repurpose What You Already Have
Before you jump on the smart home bandwagon, take a good look around your house. Can you repurpose existing devices into smart devices? For instance, you can transform many older TVs into smart TVs. All they need is the help of a budget-friendly streaming device like a Chromecast or Fire Stick.
5. Get Crafty with Automation
There are creative ways to leverage existing technology to add a touch of smarts to your home. For example, you can use smart plugs to control table lamps or coffee makers. This creates a basic level of automation. You skip the need for expensive smart appliances.
6. Leverage Free Smartphone Apps
There are a ton of free smartphone apps that can add smart functionality to your home. Many don’t even need any extra hardware. Use sleep cycle tracking apps to mimic the sunrise and sunset. Download smart weather apps. Many can trigger adjustments to your thermostat based on the forecast.
7. Explore Open-Source Options
The open-source software community offers a treasure trove of possibilities. It’s a great place for budget-conscious smart home enthusiasts. Research open-source platforms like Home Assistant. They allow you to connect various smart devices from different brands. It puts them under one central hub. This eliminates the need for expensive proprietary systems.
8. Think Security First
While affordability is important, you should never compromise security. Do your research before purchasing any smart home device. Make sure they have proper encryption protocols and security updates in place. You want to ensure they protect your data and privacy.
9. Consider Subscription Services
Some subscription services deliver smart home functionalities. These services might offer bundled features. Such as cloud storage for security camera recordings. Or access to a wider range of voice assistant routines. Carefully check the subscription costs. Weigh them against the value they provide before signing up.
10. Be Patient and Play the Long Game
Building a smart home on a budget is a marathon, not a sprint. Take your time. Research different options and focus on the features that matter most to you. New and more affordable smart home products often hit the market. You can gradually add functionality and create your dream smart home one step at a time.
By following these tips, you can transform your home into a smart haven without breaking the bank. A smart home doesn’t have to be about the latest gadgets and gizmos. It’s about utilizing technology to enhance your comfort, convenience, and security. And doing it in a way that fits your lifestyle and budget.
Need Help Building a Savvy Smart Home Network?
Are you looking for a smart home guru to help you build your dream? Our expert team is pleased to help. We’ll work with you to plan an affordable smart home deployment as well as providing expert security and technical support.
Contact us today to learn more about our smart home services.
This Article has been Republished with Permission from .